Get 24/7 incident response assistance from our global team
- APAC: +65 3159 4398
- EU & NA: +31 20 890 55 59
- MEA: +971 4 540 6400
- LATAM: +56 2 275 473 79
Get 24/7 incident response assistance from our global team
Please review the following rules before submitting your application:
1. Our main objective is to foster a community of like-minded individuals dedicated to combatting cybercrime and who have never engaged in Blackhat activities.
2. All applications must include research or a research draft. You can find content criteria in the blog. Please provide a link to your research or research draft using the form below.
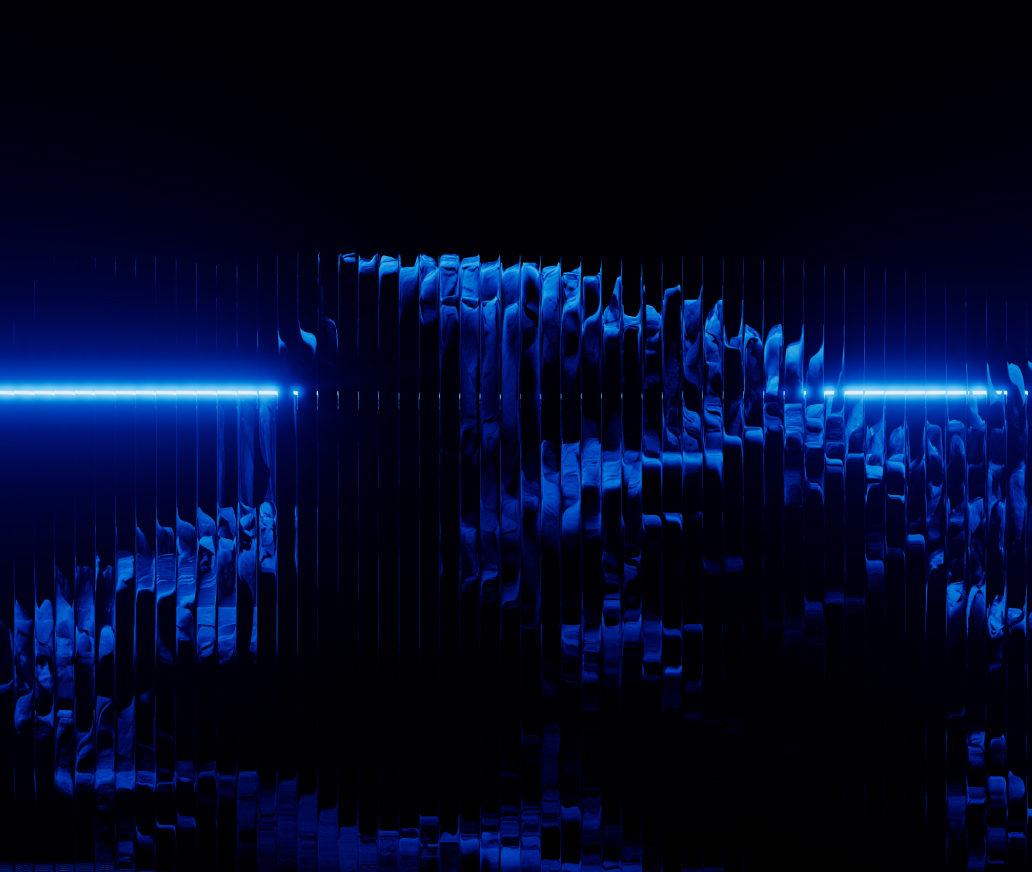
Robustly defend your critical OT and ICS infrastructure that supports national security, public welfare, and beyond through proactive threat detection, response, and mitigation powered by Group-IB full-suite cybersecurity technologies.
Industries are facing unprecedented cyber risks as adversaries increasingly target critical infrastructure. Defending these systems requires finding the right OT/ICS cybersecurity solution provider who understands legacy control systems, connected assets, and the risks unique to OT environments.
Ransomware incidents have profoundly impacted the OT/ICS threat landscape. Cybercriminals frequently exploit vulnerabilities to disrupt critical infrastructure and extort payments from organizations. Adversaries are now using ICS-specific kill lists to halt industrial processes.

of Global ICS Systems Attacked With Malware in 2022
Stop phishing emails before they deliver ransomware payloads. Deploy email protection that identifies malicious attachments, suspicious links, and social engineering tactics targeting OT personnel.

Group-IB Managed XDR can swiftly detect and isolate ransomware threats, minimizing their spread and impact. It provides 24/7 monitoring of all instances, rapidly identifying and responding to ransomware IOCs. It uses advanced analytics that could indicate a ransomware attack, ensuring rapid mitigation.

Group-IB Incident Response team helps organizations master their response tactics to ransomware attacks. Our experts have assisted industry leaders in mitigating damage, restoring systems, and conducting thorough incident investigations.

Connecting IT and OT environments creates a complex, unmanaged attack surface. Attackers often exploit blind spots such as shadow OT, unpatched vulnerabilities, and supply chain dependencies to infiltrate industrial networks and disrupt operations. Organizations need comprehensive visibility into these expanding entry points to secure critical infrastructure.

ICS vulnerabilities disclosures made across 152 vendors in 2025
Protect your industrial systems by regularly identifying vulnerabilities, assessing them, and promptly mitigating them. Obtain in-depth architecture reviews and identify security weaknesses in your devices, applications, cloud infrastructure, and more.

Map critical industrial assets and identify the specific cyber threats that could disrupt them. Group-IB Incident Response Readiness Assessment evaluates your current defenses and provides a clear roadmap to withstand industry-specific attacks and maintain seamless operations.

Simulate real-world attacks to understand how adversaries might exploit the convergence of IT and OT environments. Group-IB Penetration Testing identifies vulnerabilities in your critical assets, helping you prioritize fixes based on real threat actor tactics.

Simulate real-world attacks to understand how adversaries might exploit the convergence of IT and OT environments. Group-IB Penetration Testing identifies vulnerabilities in your critical assets, helping you prioritize fixes based on real threat actor tactics.
Unmapped OT assets and shadow IT create severe security blind spots. Without a complete, real-time inventory of your infrastructure, you cannot accurately assess risk, detect unauthorized access, or patch the vulnerabilities that can hinder manufacturing operations.

of organizations experienced at least one cybersecurity incident in 2025 through the exploitation of unknown, unmanaged, or poorly managed internet-facing assets.
Identify every internet-facing IT, OT, and ICS asset connected to your infrastructure. Group-IB Attack Surface Management continuously scans outside your network perimeter to uncover unmanaged devices and shadow IT, giving you the visibility needed to prioritize and secure exposed entry points.

Gain complete visibility over the devices operating inside your network. Group-IB Managed XDR collects telemetry across your internal environment to maintain an accurate, real-time asset inventory. This continuous monitoring enables you to detect anomalous behavior and protect critical systems from active threats.
Attackers target vendors, contractors, and managed service providers to steal credentials or hijack integrations. Industrial environments increasingly rely on remote access for third-party vendors and maintenance teams. A single compromised remote user can move laterally across flat networks and disrupt critical operations. Organizations must treat third-party vendors as extensions of their own attack surface. This means enforcing vendor risk scoring in ICS risk assessments, strict network segmentation, zero-trust controls for integrations, and continuous monitoring of tokens and APIs.

Direct losses resulted from a 2025 cyberattack on an automotive manufacturer, causing significant disruptions to manufacturing operations, supplier dependencies, and logistics networks.
Make use of Group-IB vulnerability assessment services, where our experts perform comprehensive tests on your IT systems to identify any unknown vulnerabilities that may have been missed by automated scans.

Security teams need more than generic alerts to defend industrial operations. Effective threat hunting depends on knowing which threat actors, techniques, and infrastructure are relevant to the environment, then using that context to investigate suspicious activity before it affects operations.

of organizations in 2025 experienced a successful cyber incident in OT
Focus on the adversaries actively targeting your sector and region. Group-IB Threat Intelligence maps attacker infrastructure and toolsets, enabling your team to conduct a precise ICS risk assessment and execute effective threat-hunting campaigns.

Continuously monitor the ICS network to detect intrusion attempts and intervene before attackers inflict damage. Leverage the capabilities of Group-IB Managed XDR to identify suspicious activities and anomalies, not only based on baselines but also on real-time user behavior. Additionally, Managed XDR provides a data lake for investigation and threat hunting, aiding in the search for potential threats to your IT/OT/ICS environment.

As OT cybersecurity regulations become more demanding, there's a growing emphasis on expanding compliance coverage through stronger frameworks, including risk-assessment initiatives, new security controls, updated policies and procedures, and enhanced employee training.

of organizations say they achieve compliance with security standards and guidance, reflecting a lack of confidence in OT cybersecurity
Industry regulations mandate strict safeguards for data confidentiality and system integrity. Group-IB Managed XDR provides continuous monitoring across your interconnected IT and OT environments. This ensures your critical assets remain actively protected against threats while maintaining continuous alignment with complex compliance frameworks.

Build cybersecurity awareness through a culture of regular training for all staff members. Group-IB training programs equip your OT and IT teams with the skills needed to identify emerging threats, manage risk, and execute updated security procedures effectively.

Schedule a consultation with Group-IB experts for a comprehensive ICS risk assessment. We will map your industrial attack surface and implement the controls you need to build a resilient defense against targeted attacks.