
Get 24/7 incident response assistance from our global team
- APAC: +65 3159 4398
- EU & NA: +31 20 890 55 59
- MEA: +971 4 540 6400
- LATAM: +56 2 275 473 79
Get 24/7 incident response assistance from our global team
Please review the following rules before submitting your application:
1. Our main objective is to foster a community of like-minded individuals dedicated to combatting cybercrime and who have never engaged in Blackhat activities.
2. All applications must include research or a research draft. You can find content criteria in the blog. Please provide a link to your research or research draft using the form below.

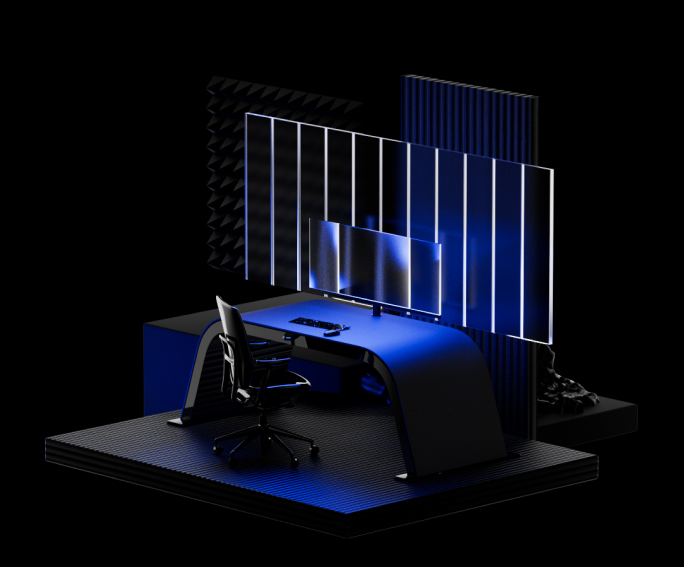
As businesses move to the cloud and adopt rapid digitization, they’re facing more complex and expansive IT infrastructures. This change makes it increasingly difficult to keep track of and secure external IT assets throughout the enterprise. The assets you don’t see leads to hidden risks that can grow over time.
Group-IB Attack Surface Management delivers external attack surface management that automatically maps every asset and provides continuous attack surface monitoring and analysis. Our platform enriches findings with threat intelligence to assess risk and prioritize issues for high-impact attack surface reduction.
Key features of Group-IB Attack Surface Management solution
Stay ahead of your expanding digital footprint and gain actionable insights to improve security posture

Discover all external assets, including shadow IT, forgotten infrastructure, and misconfigurations

Automate IT asset discovery and continuously map out your organization’s external attack surface

Confirm your organization’s assets to generate an up-to-date IT asset inventory that keeps up with growth

Gain insights into hidden risks like credential dumps, dark web mentions, botnets, malware, and more
Check confirmed assets for common vulnerabilities & assign each one a risk score to prioritize remediation
Reduce risk and fix issues that provide measurable results for your security program
Access industry-leading threat intelligence data including malware analysis, botnet tracking, phishing detection, credential dumps, dark web mentions, and more

Customize your notification settings to receive alerts when you need them. Set up reporting to meet your needs and show meaningful results to your stakeholders

Increase the return on existing security investments and gain measurable ROI with automated asset discovery that frees up resources for other priorities
Attack Surface Management is the continuous process of discovering, inventorying, assessing, and securing an organization’s security perimeter and all of the Internet-facing assets within their digital estate. It’s worth emphasizing that attack surface management is not a short-lived task or project, but an ongoing and recursive process that is fundamental to every organization’s cybersecurity program.
As the name suggests, the attack surface is any aspect of an organization’s digital presence that is accessible from the Internet and can therefore be probed for weaknesses by threat actors. It may be helpful to think of your attack surface as the sum of all potential attack vectors that cybercriminals could use to breach your corporate network. Managing the attack surface is an effective way to reduce risk and improve security posture.
Attack Surface Management is also an emerging product class that simplifies and streamlines the ASM process for customers. It automates several steps, including IT asset discovery, risk assessment, and the prioritization of issues based on the risk they present to the organization. By deploying the Group-IB ASM solution, you can save time that would otherwise be dedicated to these steps, which makes the attack surface management process more efficient and frees up resources to focus on other high priority projects.
External Attack Surface Management is the process of continuously discovering, inventorying, assessing, and securing all of the external IT assets that an organization owns. An IT asset is considered external if it can be accessed from the public Internet without the use of a VPN.
External Attack Surface Management is generally considered a specific subset of the broader concept of attack surface management. Other adjacent categories include “cyber asset attack surface management,” which covers IT asset discovery and management for both internal and external assets, and “cloud security posture management,” which is a flavor of attack surface management focused exclusively on cloud assets.
The precise definitions of these terms are still up for discussion. As technology and markets evolve, some of these terms will coalesce and others will simply fall out of fashion. The important thing to understand is that external attack surface management is an essential security process that discovers, catalogs, assesses, and secures all external IT assets.
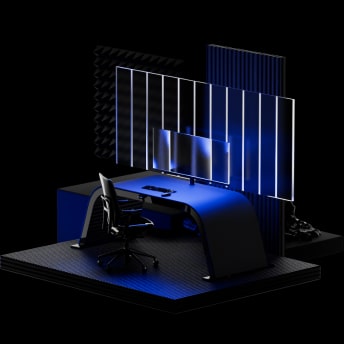
Group-IB scans the entire Internet to identify and index corporate infrastructure. Relationships between these assets are then mapped out through digital connections like subdomains, SSL certificates, DNS records, and other discovery techniques. When you enter your organization’s domain, the system can immediately identify your infrastructure. This is then enriched with real-time discovery techniques and security validation to identify issues and raise alerts for remediation.
The focus of Group-IB Attack Surface Management is to identify your full attack surface, including the external assets you do not know about, such as shadow IT, forgotten infrastructure, and misconfigured databases that are accidentally exposed to the open web. This is distinct from vulnerability scanners, which must be given a specific IP range of known assets to function.
Group-IB Attack Surface Management provides value in several ways. First, it identifies unmanaged assets, which greatly reduces risk and improves security. Second, these newly discovered assets can be added to the scope of existing security investments, such as vulnerability scanners, penetration tests, and even newer tools like BAS and CART products. Lastly, by automating the process of identifying and inventorying external assets. The teams and personnel that would ordinarily spend a significant amount of time on these tasks are free to reallocate resources to other high-priority projects.
Group-IB has been scanning the dark web and collecting threat intelligence for more than a decade. This includes credential dumps, discussions on dark web forums, malware deployment, the hosting of phishing panels, the sale of initial access to corporate networks, C&C server traffic, botnet activity, and more. When you deploy Group-IB Attack Surface Management, your organization and all of its confirmed assets are checked against these databases to see if there are any matches. If there is a match, the data is added to that asset in your Group-IB Attack Surface Management dashboard.
Contact the Group-IB team via the form at the bottom of this page to get started with a trial license. Attack Surface Monitoring doesn’t require any new instances and is deployed in a matter of minutes. All you need to test drive Group-IB Attack Surface Management is your corporate email address.
Once you have access to Group-IB Attack Surface Management, it takes just a few clicks to map your entire company attack surface. No agents, integrations or major configurations are required.
No, Group-IB Attack Surface Management conducts passive data collection.
Pricing for Group-IB Attack Surface Management is based on the organization’s total number of domains, sub-domains, SSL certificates, and IP addresses, making attack surface monitoring accessible to companies of all sizes and scope. Licenses are typically 1 year in length, although longer licenses are available at a discounted rate.